Prerequisites¶
projectx-prod-vpchas been created with subnets configured.My-Desktop-Key-Pairkey pair exists.- AWS CLI configured with appropriate IAM credentials.
Note
This guide defends against the Insecure IAM Permissions attack scenario. AWS Config rules detect overly permissive roles, wildcard permissions, and risky PassRole configurations before they can be exploited.
Network Topology¶

Overview¶
AWS Config continuously records and evaluates configurations of your AWS resources against desired rules. When a resource violates a rule, Config records a compliance finding and can notify you via Amazon SNS.
AWS Config can also automatically remediate instances that violate rules AWS Systems Manager Automation via a SSM Automation document.
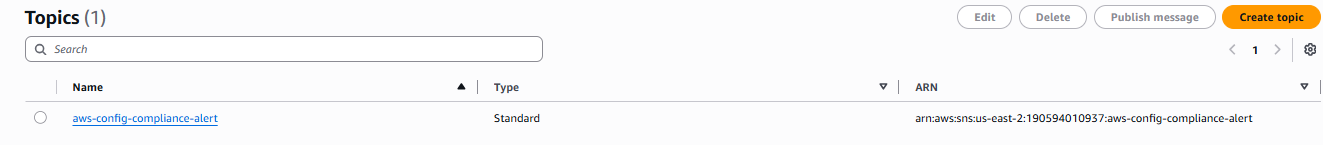
Step 1: Create an SNS Topic¶
Create an SNS topic to receive AWS Config compliance notifications. You can subscribe with email, Lambda, or other targets.
Open Amazon SNS ➔ Topics ➔ Create topic
Type: Standard
Name: aws-config-compliance-alerts
Create topic
Next, select "Create subscription" to assign an email address to get email notifications.
Select Create subscription
Topic ARN: Choose ARN:aws-config-compliance-alerts
Protocol: Email
Endpoint: Email address.
Confirm the subscription from your inbox.
Step 2: Enable AWS Config¶
Open AWS Config ➔ Getting started (or Settings)
Recording Method:
- Turn on Specific resource types
- Resource types to record: Select All globally recorded IAM resources (or narrow to IAM: AWS::IAM::*)
- Delivery frequency: Choose Daily.
- Amazon S3 bucket: Create a new bucket or use an existing one (e.g.
my-config-bucket-<account-id>). Here we could choose our datalake S3 bucket, if we wanted to get the logs and create detections in Wazuh.
Delivery method
- SNS topic: Select your aws-config-compliance-alerts topic
Refer to Step 3 below with the specific configurations names.
Confirm and Confirm again
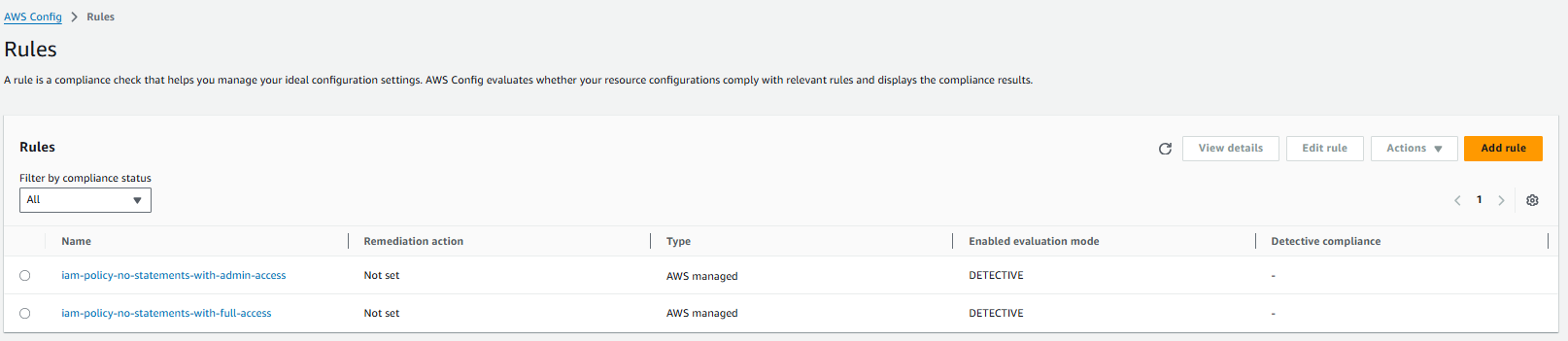
Step 3: Add IAM Config Rules¶
Add managed rules that detect the IAM misconfigurations from Insecure IAM Permissions.
Rule 1: Detect Admin-Level Policies¶
Detects IAM policies that grant full administrative access (e.g. *:* or AdministratorAccess), as in the admin role scenario.
AWS Config ➔ Rules ➔ Add rule
Search for iam-policy-no-statements-with-admin-access
Add rule ➔ Name: iam-policy-no-statements-with-admin-access
Save
Rule 2: Detect Full Access to Services¶
Detects policies that grant full access to specific services (e.g. s3:*, ec2:*), as with the EC2 instance role in Scenario 2.
Console
Add rule
Search for iam-policy-no-statements-with-full-access
Add and save
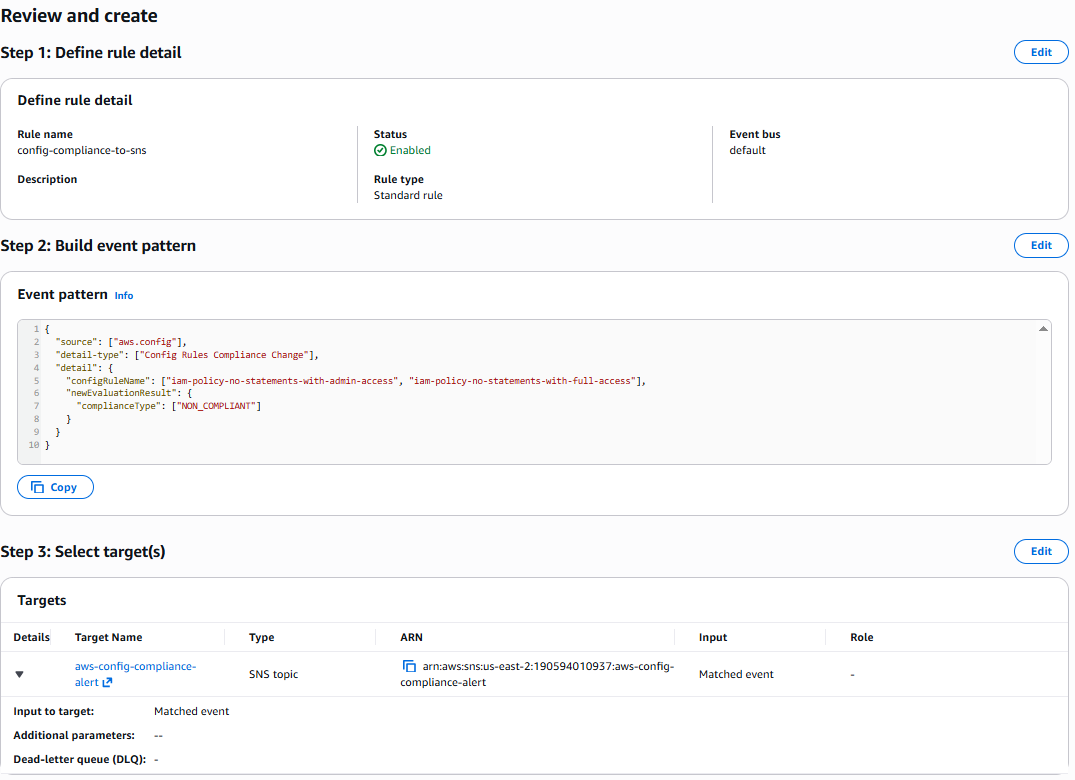
Step 4: Send Compliance Changes to SNS¶
To receive SNS notifications when compliance changes (a resource becomes NON_COMPLIANT), configure an Event-based rule or rely on Config’s built-in notifications.
AWS Config sends an SNS notification when the Configuration Snapshot is delivered (daily for us, since we set the frequency to daily)
- The snapshot includes compliance status; you can parse it or use Config Aggregator / Security Hub for filtering.
Event-driven notifications
For near-real-time alerts, use Amazon EventBridge to react to Config compliance change events:
Open Amazon EventBridge ➔ Rules ➔ Create rule
Name: config-compliance-to-sns
Rule type: Event pattern
Event pattern:
{
"source": ["aws.config"],
"detail-type": ["Config Rules Compliance Change"],
"detail": {
"configRuleName": ["iam-policy-no-statements-with-admin-access", "iam-policy-no-statements-with-full-access"],
"newEvaluationResult": {
"complianceType": ["NON_COMPLIANT"]
}
}
}
Target: SNS topic aws-config-compliance-alerts
Create rule
When any of these rules find a resource NON_COMPLIANT, EventBridge forwards the event to SNS, and your subscribers receive an alert.
Verify Setup¶
Deploy the insecure-iam-permissions Stack. The admin role and wildcard policies should appear as NON_COMPLIANT.
Navigate to AWS Confg ➔ Rules ➔ Select a rule ➔ View results: After Config evaluates (can take several minutes to hours), you’ll see compliant/non-compliant resources.
Cleanup¶
Warning
Disable AWS Config and remove resources when finished to avoid ongoing charges.